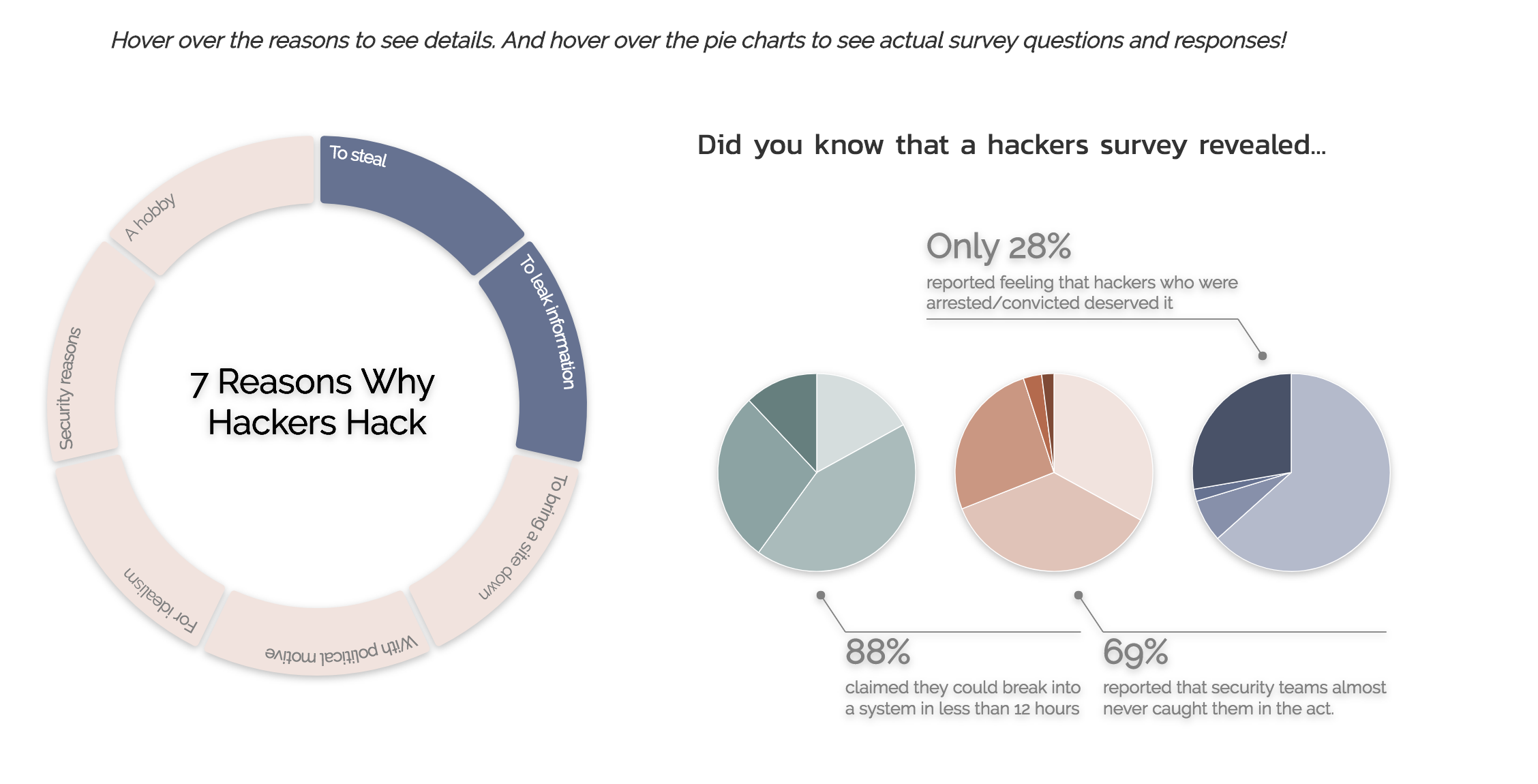
Cyber Security Crimes, Ethics and a Suggested Algorithm to Overcome Cyber-Physical Systems Problems (CybSec1)
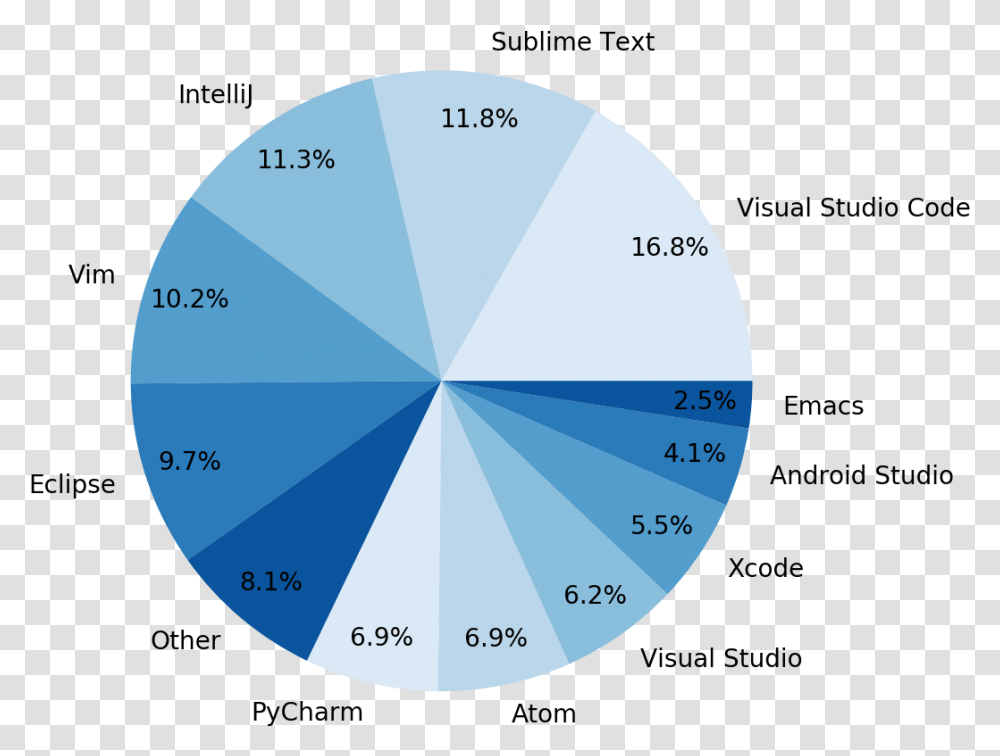
The Rise Of Microsoft Visual Studio Code Hacker Noon Visual Studio Code Market Share, Sphere, Diagram, Outer Space, Astronomy Transparent Png – Pngset.com
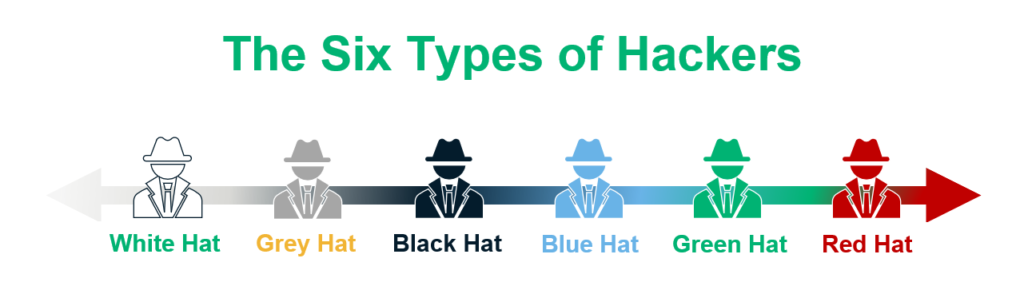
White hat Metasploit Project Exploit Computer security Penetration test, Framework, logo, payload png | PNGEgg
PDF) Overview of Ethical Issues such as security, confidentiality and Hacking in software engineering