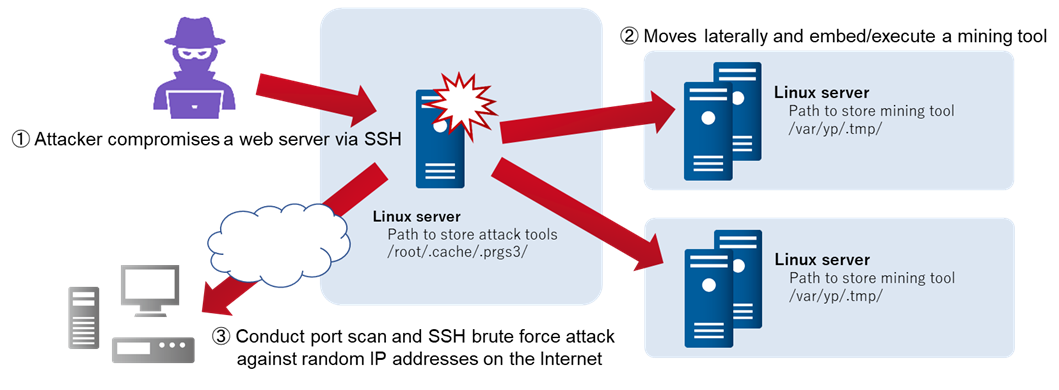
Attacks Embedding XMRig on Compromised Servers - JPCERT/CC Eyes | JPCERT Coordination Center official Blog
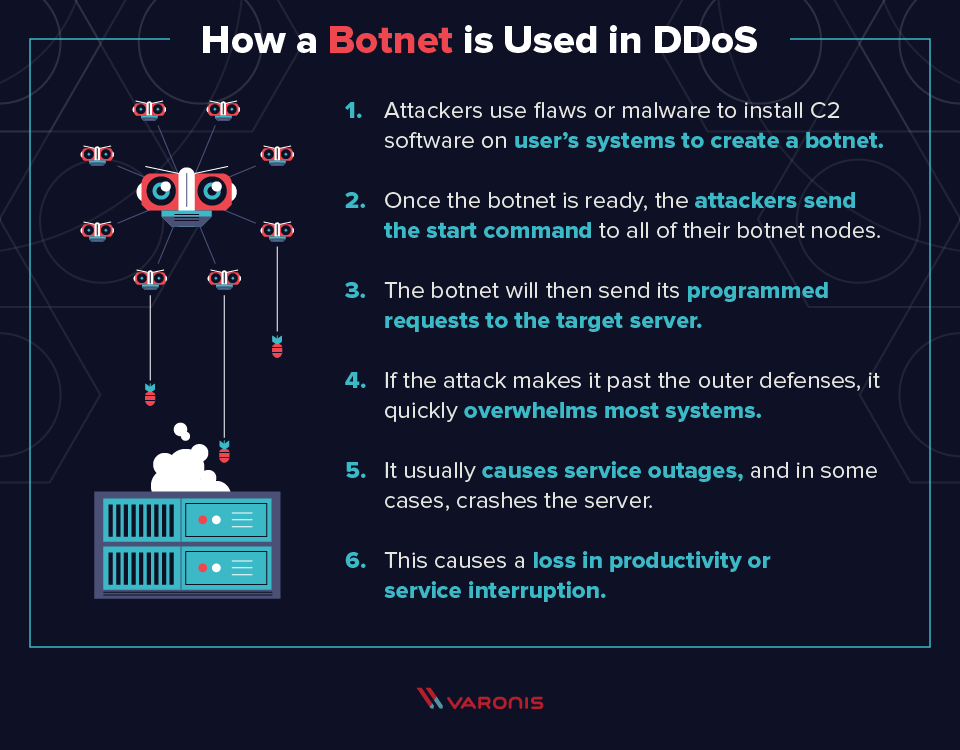
A simplified model of a botnet conducting a DDoS attack. Once an army... | Download Scientific Diagram

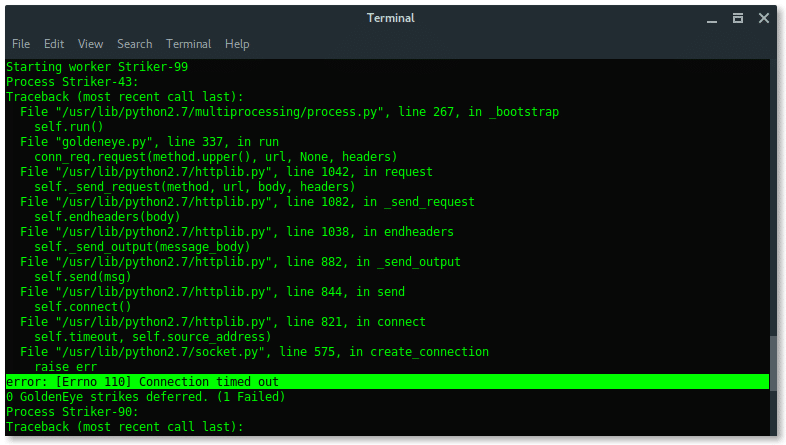
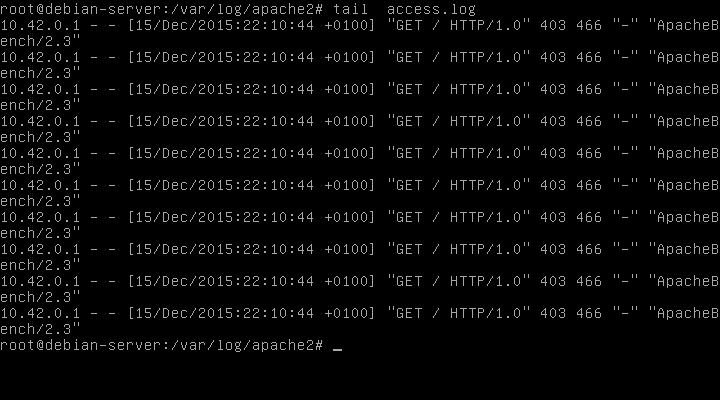
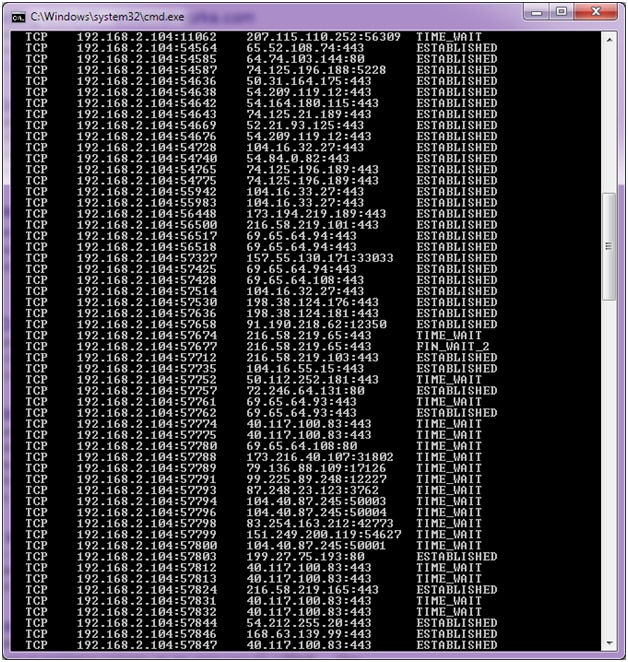
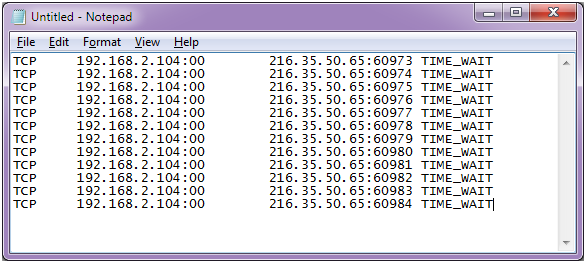
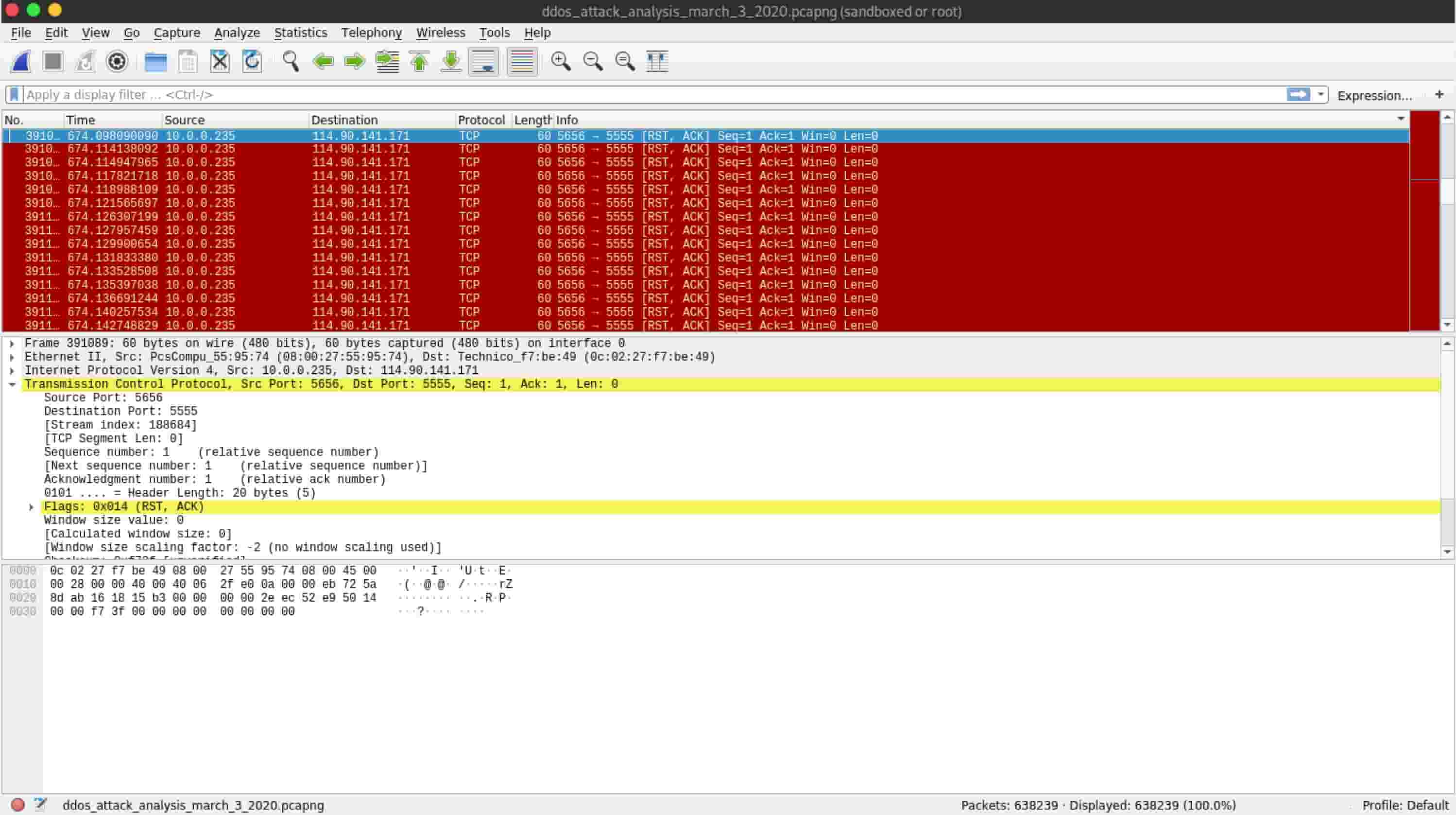
How to quickly check to see if your Linux server is under a DoS attack from a single IP address | TechRepublic
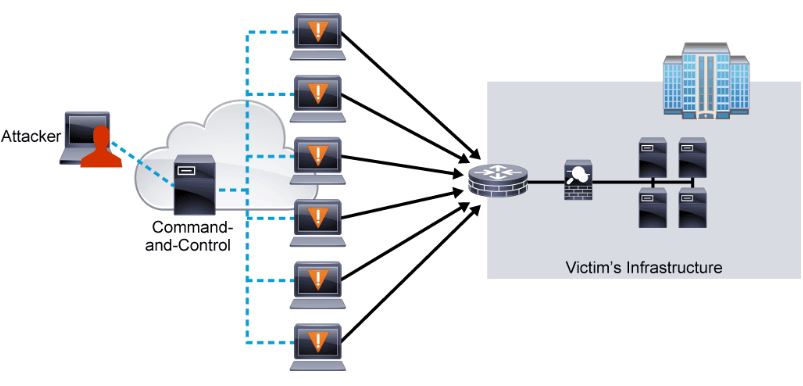
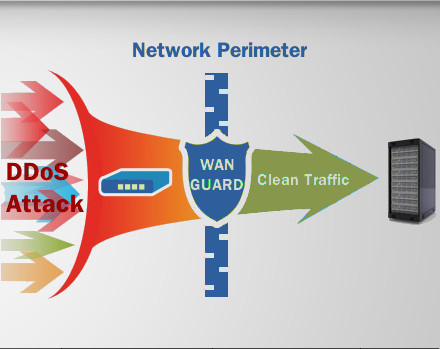
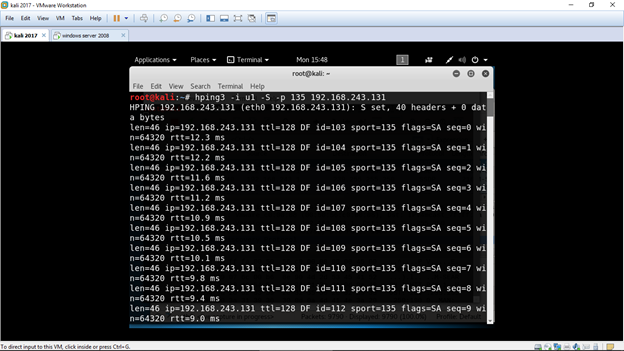
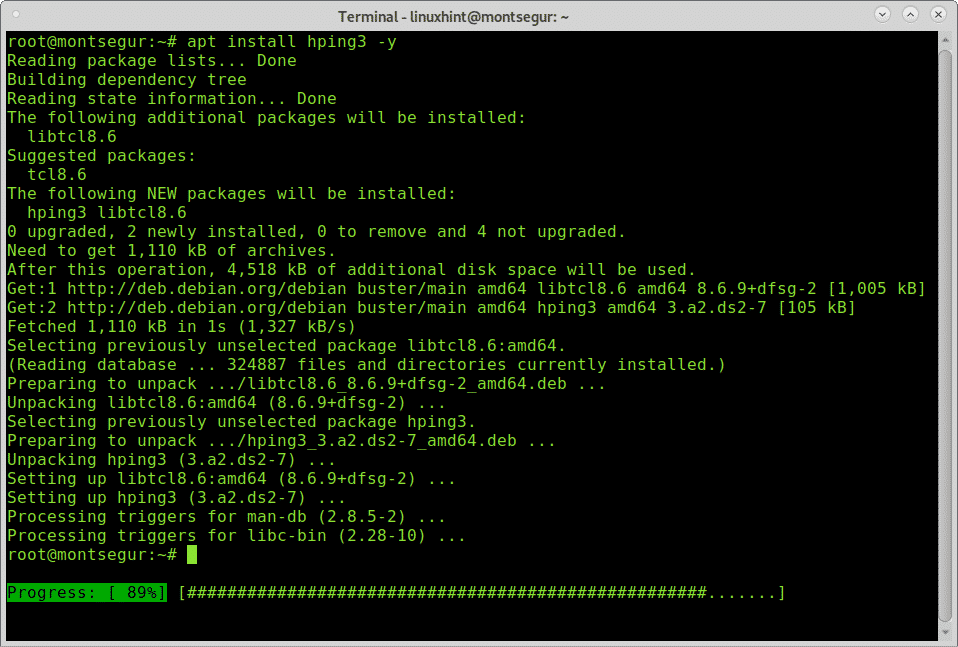
DoS and DDoS attack-The Ultimate goal for CCNA, Cisco Networking, Cisco Certification Exam, Linux Installation and Server Management