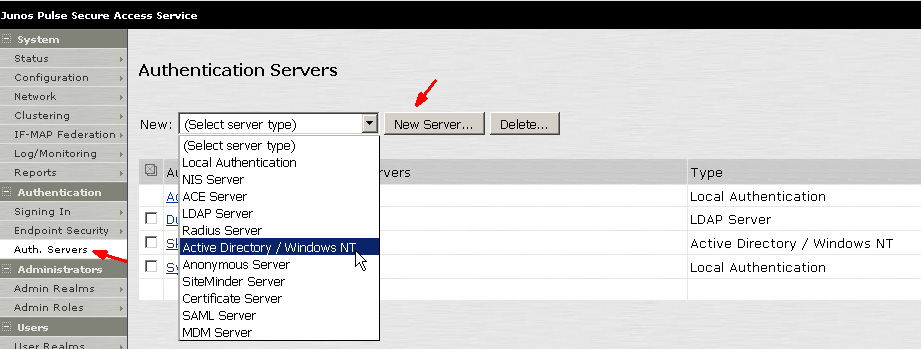
Pulse Secure Juniper SSL VPN Setup Additional Authentication Servers (2) – IT Network Consulting | Design, Deploy and Support | San Diego
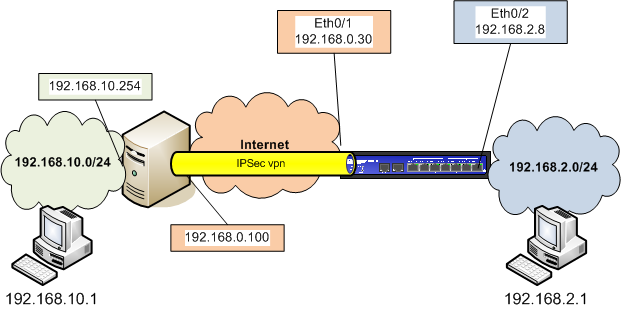
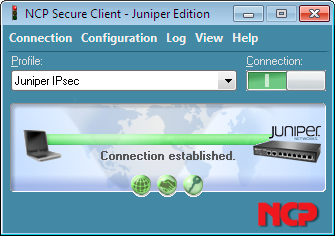
IPSec VPN between Windows Server 2008 and Juniper ScreenOS | Corelan Cybersecurity ResearchCorelan Cybersecurity Research

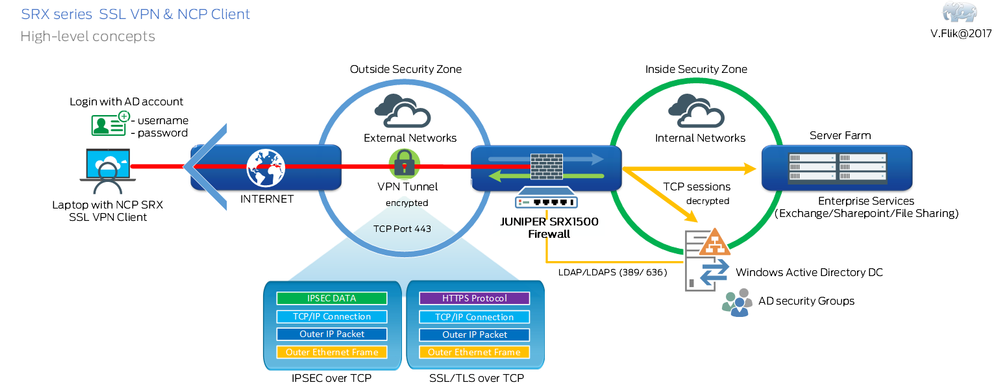
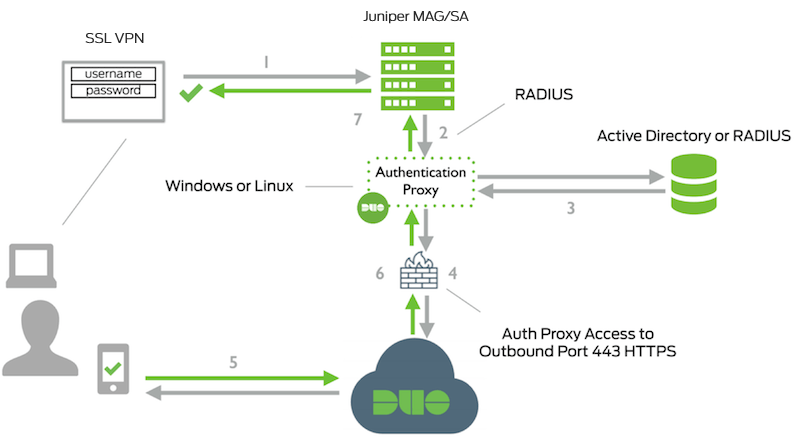
Juniper Networks Virtual private network IPsec Tunneling protocol SSL VPN, vpn network diagram, angle, text, light png | PNGWing

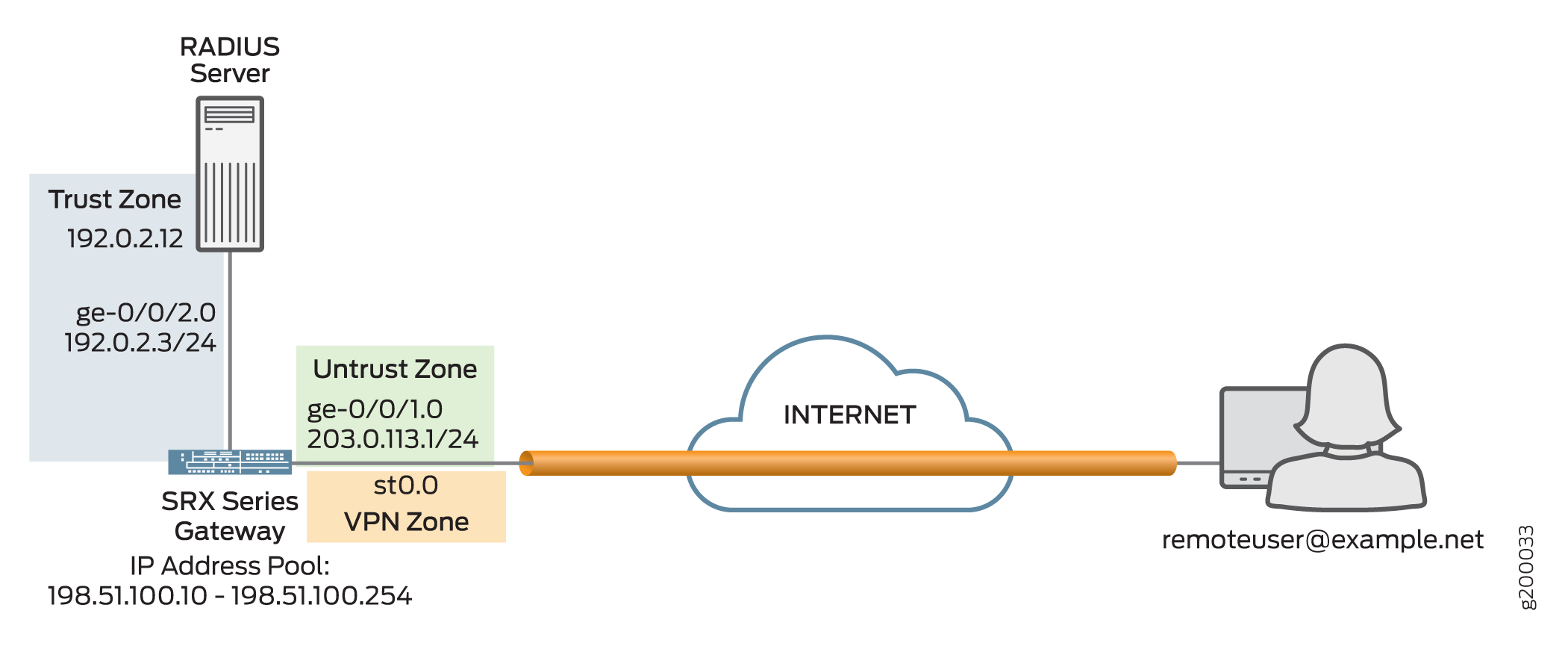
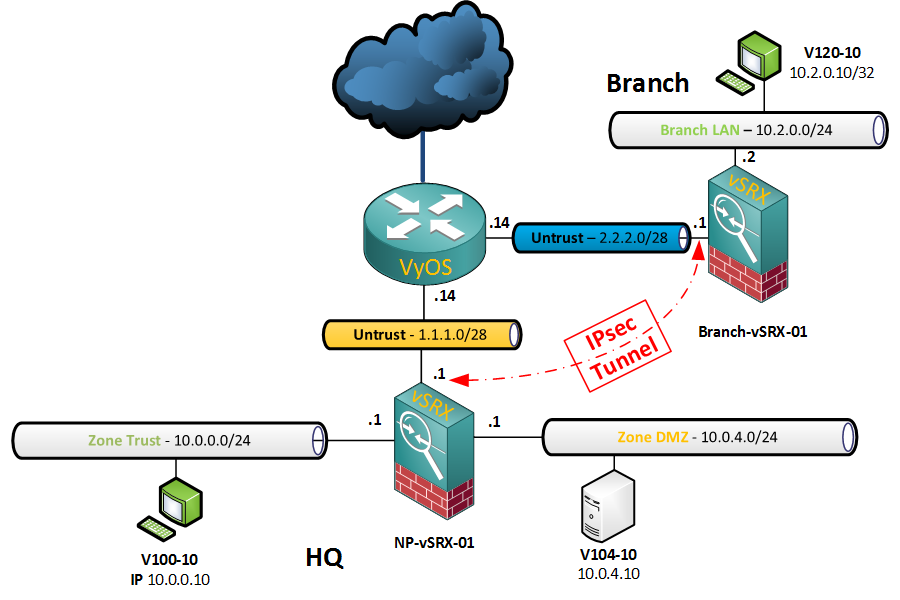
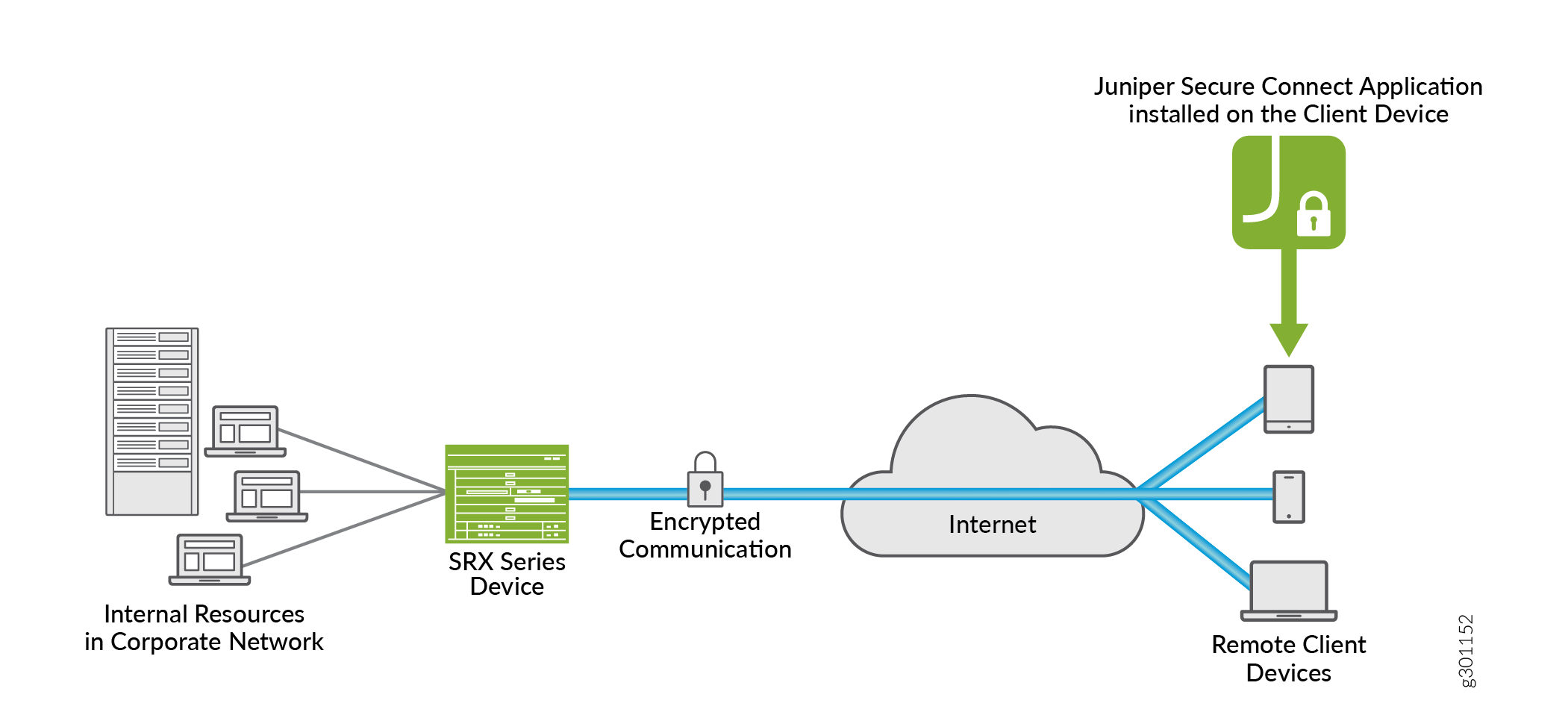
![SRX] Pulse client is connected, but can't get to protected resources - Juniper Networks SRX] Pulse client is connected, but can't get to protected resources - Juniper Networks](https://kb.juniper.net/library/CUSTOMERSERVICE/GLOBAL_JTAC/dynamic_vpn/topology_both_single_picIPnetwork.bmp)